There are 40 different application for the Windows platform that have a serious security flaw that can only be patched if all 40 developers individually patch the flaw in their own apps. One Microsoft patch won’t do the job, according to HD Moore, chief security officer for Rapid7 a company that creates an open-source security evaluation tool.
Unfortunately, the list of 40 applications has not been revealed by Moore, but he said that they consist of a wide range of Windows applications†including the Windows shell program Explorer.exe. The flaw also existed in iTunes for Windows, but Apple has already patched it in the version 9.1 update that came down the pipe a month ago.
While Moore would not give specific details about the flaw, he did say that an attack could happen if a Windows DLL file was loaded over a network when the file is shared. So, if you share a file on one computer with other computers on a local or Internet network, then the flaw could affect one of the applications. He said it was similar to the problem that surface awhile back in how Windows Shortcuts could be used to infect a system.
The best way to avoid this problem is first, avoid using Internet Explorer 6. The old browser that shipped with Windows XP is riddled with security problems and should be updated to IE8 immediately. Secondly, using Windows XP makes one more vulnerable than if a user is on Windows 7. That is a bigger upgrade, but it would be advisable to do so as soon as one can in order to avoid this flaw. But even those steps are not enough. The third thing to do is … block outbound SMB by blocking TCP ports 139 and 445, and disable WebDAV client to prevent these flaws from being exploited from outside the their local network,†said Moore. But how does one do this? This is a very technical process, but here are the step-by-step instructions for Windows 7. They will be similar in previous versions of Windows.
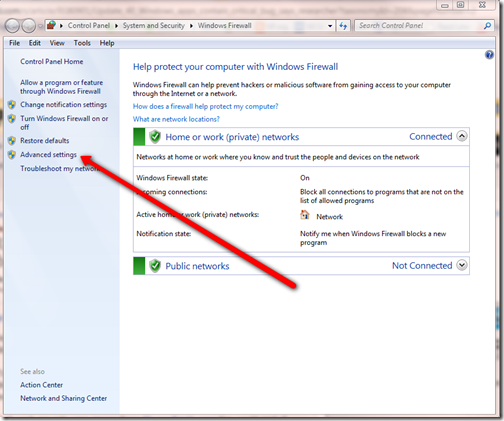
First open Windows Firewall and click on Advanced Settings.
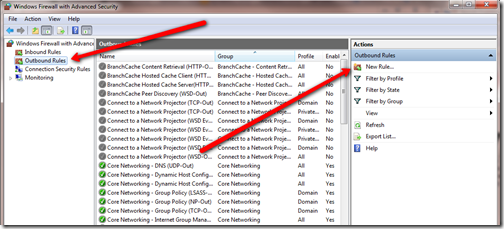
Next click on Outbound Rules item in the left hand list. These are rules that keep the computer being used from infecting others on the network. This will have to be done on each system on the local network.
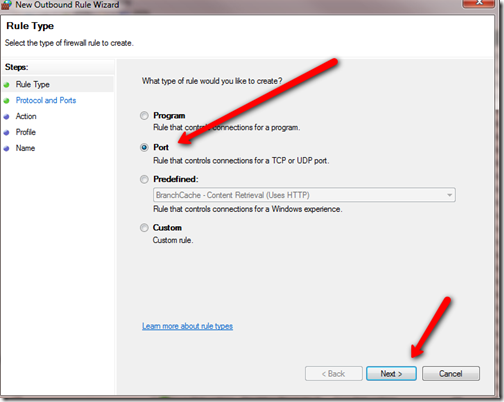
Then click on the New Rule item on the right side. In the resulting dialog box, make sure Port is selected and click Next.
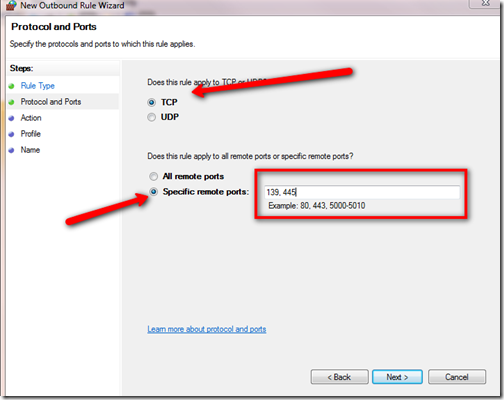
A new box will open. Choose TCP at the top and Specific remote ports: at the bottom.
In the box next to the Specific remote ports: item enter “139, 445” exactly as shown above. This will affect file sharing on the network, so if after doing this you have trouble sharing files, you may want to temporarily disable this rule. You will do this in Windows Firewall. A list of rules is shown when it is first opened. Find the rule that you will name later in this this How To and uncheck it.
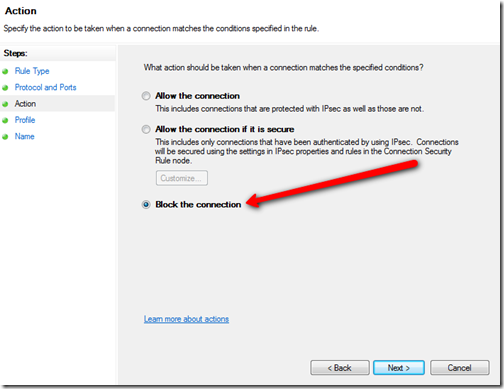
Now click Next and be sure that Block Connection is chosen on the next screen.
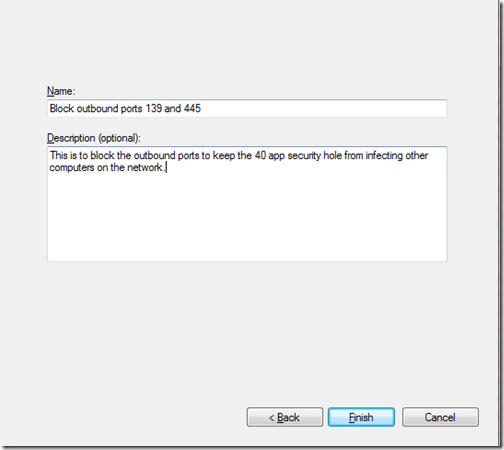
Click on Next, select all three check boxes and then choose Next again. Give this new rule a name and describe it.
Finally, click on Finish. The ports are now blocked. Follow these steps on all your other computers.
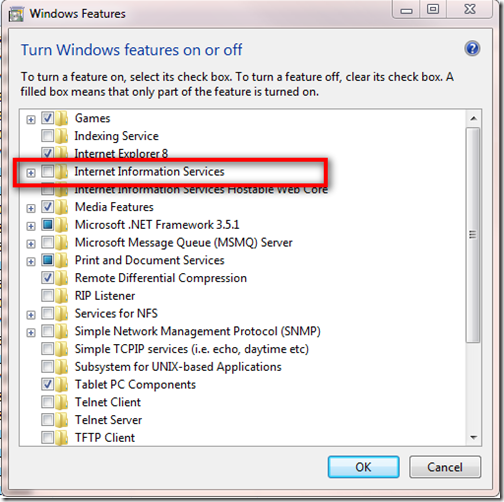
The next thing is to disable WebDAV, if it is enabled. This is only needed if you have something called IIS enabled. This is not enabled by default so almost no one will need to do this. To check, simply open the Programs and Features item under Programs in your Control Panel. Wait for the list to populate and look for an item called Internet Information Services.
Notice that it is unchecked. This is how the vast majority will find their systems. But if you do have it checked, then follow the instructions on how to disable WebDAV from the Microsoft Knowledge Base item 241520.
Until this vulnerability is patched by both Microsoft and all of the other software developers that are affected, this is the only sure way to avoid being affected other than unhooking from any networks altogether.
Source: Computerworld via betanews.